.png?width=1728&height=836&name=1%20(5).png)
The Health Insurance Portability and Accountability Act (HIPAA), enacted in 1996, is a federal law establishing nationwide standards to safeguard sensitive patient health information to ensure it is not disclosed without the patient's awareness or consent. Explore details about this U.S. regulation and learn about how to comply.
What is the Health Insurance Portability and Accountability Act (HIPAA)?
The Health Insurance Portability and Accountability Act was initially focused on addressing insurance coverage gaps for individuals transitioning between jobs. Without this legislation, individuals would have risked losing their insurance coverage during job transitions.
Another objective was to guarantee the proper security of all data, preventing unauthorized individuals from accessing healthcare information. HIPAA is applicable within the United States and is governed by the Department of Health and Human Services' Office for Civil Rights (OCR).
Purpose of HIPAA
HIPAA was established to modernize the exchange of healthcare information and ensure the protection of Personally Identifiable Information collected by healthcare and insurance entities, safeguarding it from fraud and theft and preventing unauthorized disclosure.
Patient healthcare information is handled with increased sensitivity, allowing swift access by different healthcare providers. HIPAA laws and regulations mandate enhanced security measures to prevent data leakage. For comprehensive guidance on HIPAA regulations and compliance, you can refer to HIPAA Journal, an excellent resource with a detailed checklist for your compliance journey.
What is Protected Health Information (PHI)?
Any entity or individual handling Protected Health Information (PHI) must comply with HIPAA. PHI is formed when health data is linked with personally identifiable information, encompassing:
- Geographical identifiers
- Names
- Email addresses
- Phone and fax numbers
- Account numbers
- Medical record numbers
- Website URLs
- Vehicle information
- Social security numbers
- Retinal, voice prints, and fingerprints
- Device information, IP addresses
- Beneficiary numbers for health insurance
- Full face photographs
- Certificate and license numbers
When stored electronically, PHI is referred to as ePHI.
The Scope of HIPAA
The Health Insurance Portability and Accountability Act applies to various entities routinely handling Protected Health Information. These include:
- Healthcare providers
- Business associates
- Healthcare clearinghouses
- Health plans
HIPAA Law & Regulations
HIPAA comprises the following regulatory rules:
.png?width=1728&height=836&name=2%20(4).png)
- Privacy Rule: Defines how, when, and under what circumstances you can use and disclose PHI. Limits the use of patient information without prior consent. Patients can request copies of their health records and corrections.
- Security Rule: Sets standards to protect electronic PHI (ePHI). Applicable to anyone working with ePHI. Requires risk assessments and audits by Security and Privacy Officers to identify threats to PHI integrity.
- Breach Notification Rule: Mandates notifying the Department of Health and Human Services and affected individuals in case of a data breach. Press releases are required if over five hundred patients in a specific jurisdiction are affected.
- Omnibus Rule: Part of the HITECH Act (2009) to encourage electronic health record use. Prohibits using PHI for fundraising or marketing without authorization.
- Enforcement Rule: Focuses on determining fines for breaches—lower fines for negligence; significantly higher penalties for violations due to willful neglect.
Individual Rights under HIPAA Privacy Rule
Within the HIPAA Privacy Rule framework, individuals possess legal entitlements to view and obtain copies of their medical information.
Individuals have the right to:
- Amend PHI
- Access PHI
- Request restrictions on the use and disclosure of PHI
- Request an accounting of disclosures
- Request confidential communications
- File a complaint
Despite patients' right to access their records, certain types of information are precluded from the Right to Access.
The excluded information encompasses:
- Safety activity records
- Quality improvement or assessment records
- Management and business records
- Information compiled for use in criminal, civil, or administrative proceedings or actions
- Psychotherapy notes
Types of HIPAA Violations
A breach of HIPAA occurs when a HIPAA entity or a business associate fails to adhere to any of the HIPAA Rules. The Department of Health and Human Services' Office for Civil Rights (OCR) and state attorneys general administer penalties for HIPAA violations. HIPAA employs four penalty categories:
.png?width=1728&height=836&name=3%20(4).png)
The Most Common Risks Associated with HIPAA
Unencrypted Data
While not mandatory, encrypting data is highly recommended by HIPAA. Even during a data leak, encrypted information remains inaccessible without proper authorization.
Unauthorized Access
Employees without proper authorization may access and review sensitive information. Establish and communicate security policies, ensuring that employees are well-informed and compliant.
Keeping Unsecured Records
Employees may leave sensitive documents unattended at their desks or neglect to use passwords for accessing digital data. Ensure the workspace is secure and passwords are consistently employed within your company.
Sharing PHI
Awareness is key when it comes to sharing sensitive information. Employees may inadvertently share PHI with colleagues. Educate them on proper data handling, emphasizing that only authorized individuals should access such data.
Loss or Theft of Devices
Devices holding valuable information can be lost or stolen. Encrypting your data prevents unauthorized access, even if a device is lost.
Lack of Employee Training
Employees may not be aware that they are working with PHI, posing risks to the company and patients. Regularly educate employees on what PHI and HIPAA entail and the consequences of violations.
Insider Threats in Healthcare
As highlighted earlier, breaches often result from errors employees make—misplacing a device, falling prey to a phishing campaign, or engaging in informal discussions about patients with colleagues. HIPAA violations can easily occur, and insider threats may manifest as unintentional or malicious. Notably, 56% of incidents involving insider threats are linked to the employee’s negligence. From March 2022 to March 2023, the healthcare industry experienced the highest average data breach cost, amounting to nearly 11 million U.S. dollars.
How To Secure Health Information for HIPAA Compliance?
Understanding and addressing the key components of the HIPAA laws and regulations is essential for ensuring the integrity, confidentiality, and availability of health information while meeting the compliance standards set forth by this vital legislation.
Complying with HIPAA involves navigating a comprehensive set of regulations to safeguard the security and privacy of individuals' health information. To adhere to HIPAA guidelines, organizations must establish robust measures for safeguarding electronic protected health information (ePHI).
- Advanced Encryption: Ensure traffic encryption within your company's network using AES 256-bit encryption, providing a robust defense against unauthorized access to data. This crucial security measure aligns with HIPAA's stringent requirements for protecting electronic protected health information (ePHI). Additionally, adopt comprehensive security policies and designate authorized personnel for accessing PHI.
- Robust Authentication and Authorization: Implement stringent controls for authentication and authorization. Restricted to approved individuals within specific organizations and teams, you can ensure that only authorized personnel can access or grant specific information and permissions. This aligns seamlessly with HIPAA's mandate to control access to ePHI, bolstering overall data security.
- Secure Business VPN: A business VPN imposes restrictions on access, introducing an additional layer of control. This stringent limitation guarantees authorized personnel access to sensitive information exclusively through secure channels, perfectly aligning with HIPAA's emphasis on controlled access to ePHI.
How to Simplify HIPAA Compliance with PureDome
Amid the increasing prevalence of remote and hybrid work arrangements, achieving compliance with regulatory standards has become progressively intricate. As an integral component of PureDome, our primary commitment centers around furnishing a comprehensive array of top-tier cybersecurity solutions, guiding you in attaining and sustaining compliance standards.
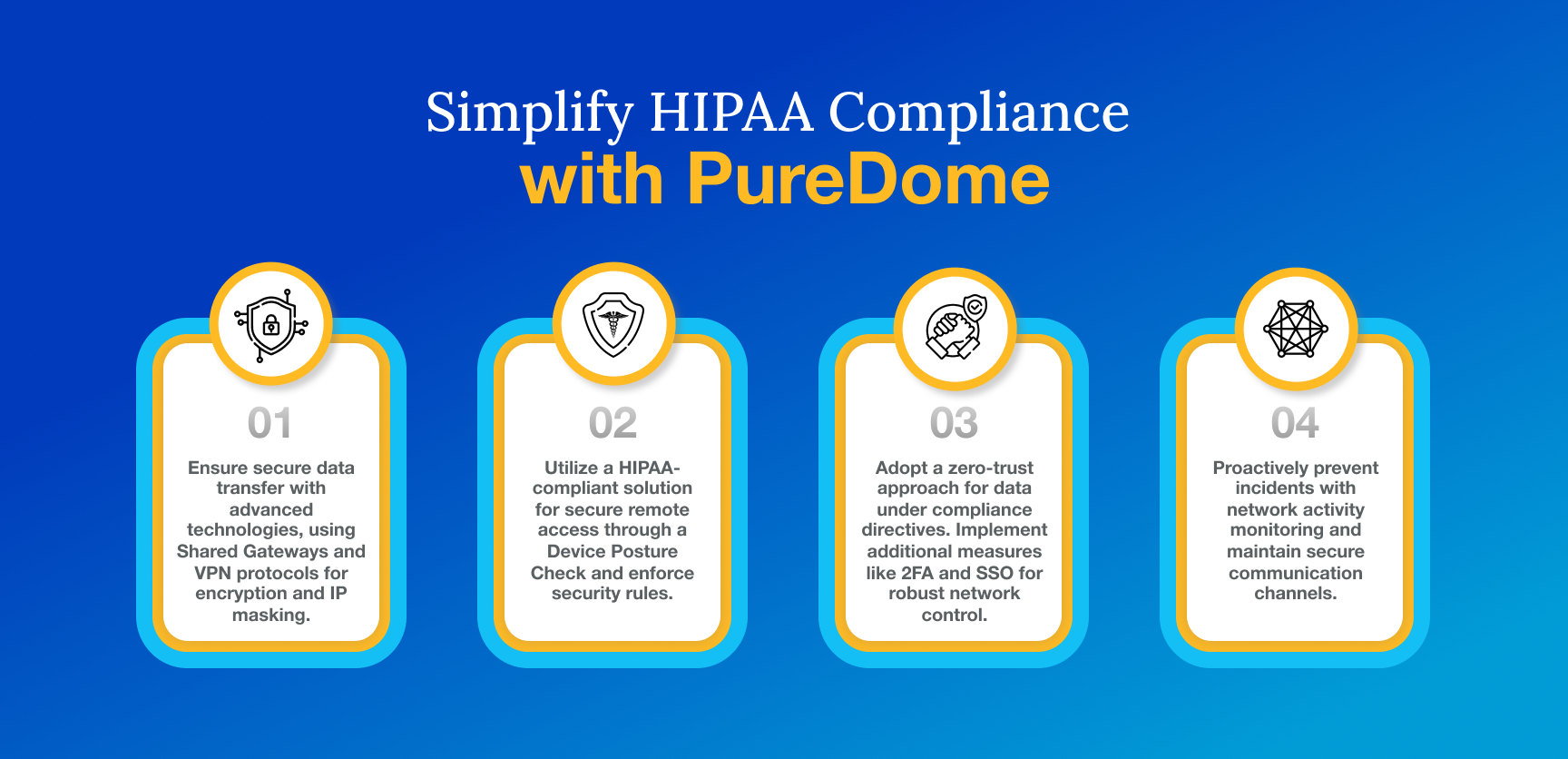
Here is how PureDome can help you achieve compliance.
- Continuous Data Encryption: Utilizing advanced technologies, PureDome consistently ensures the confidentiality of data during its transfer. Shared Gateways, equipped with advanced VPN protocols, ensure encrypted data transfer and IP masking on the open internet.
- Device Posture Checks: Continuous inspection of devices enhances your capacity to assess the overall security and health of the network. Our HIPAA-compliant network security solution fortifies secure remote access with a Device Posture Check. Evaluate users' devices based on predefined security rules and provide notifications for non-compliant devices.
- Zero Trust Approach: To secure data governed by compliance directives, PurrDome adopts a zero-trust approach. This involves implementing additional confirmation measures, such as 2FA and SSO, to ensure robust and secure network control.
- Effective Monitoring and Logging: Proactively prevent and investigate incidents by monitoring network activity and maintaining secure communication channels. PureDome facilitates the scrutiny of usage logs, identifying users of secured connections and detailing the timing of their usage.
Conclusion
HIPAA compliance is a pivotal element within the healthcare sector, incorporating an extensive array of standards and regulations crafted to protect patient privacy, secure electronic health information, and advance administrative simplification. This regulation is crucial in safeguarding individuals' sensitive health data, fostering trust in the healthcare system, and enhancing overall operational efficiency. Compliance with the standards articulated in HIPAA enables healthcare organizations to fulfill legal obligations and plays a critical role in fostering a secure, patient-centric, and streamlined healthcare environment.
.png?width=1728&height=836&name=4%20(1).png)